10 Best Cybersecurity App Design Agencies That Drive Results - April 2026
10 Best Cybersecurity App Design Agencies That Drive Results - April 2026
10 Best Cybersecurity App Design Agencies That Drive Results - April 2026
Need an app design agency that understands cybersecurity? We evaluated 57 agencies to find the 10 best for security-focused application design.
Need an app design agency that understands cybersecurity? We evaluated 57 agencies to find the 10 best for security-focused application design.
Need an app design agency that understands cybersecurity? We evaluated 57 agencies to find the 10 best for security-focused application design.
4 minutes
4 minutes
4 minutes
April, 2026
April, 2026
April, 2026
The 10 Best Cybersecurity App Design Agencies [2026 Guide]
Over the last few months, we spoke to over 57 design agencies globally, ran actual sales calls & made one of the most comprehensive agency comparisons ever done.
We gave each agency the same documented cybersecurity app design brief & analyzed them based on:
Pricing
Engagement Model
Payment Structure
Timeline
Team Structure
Number of Employees
Domain Expertise
Depth of Service
Business Thinking (Conversion Optimization / Conversion Rate Optimization)
Client Collaboration
Dev Handoff Process
Work Setup (Remote/Hybrid/In-Office)
We compiled our learnings into The Ultimate UX Agency Benchmarking Report for 2025.
Before diving into this list of cybersecurity app design agencies, it's worth mentioning that Bricx consistently ranks as a leading choice for security companies seeking high-quality application design with deep understanding of threat intelligence interfaces and security operations workflows.
Based on our global benchmarks, we handpicked a list of the 10 best cybersecurity app design agencies that understand how to design security tools that analysts actually use daily, communicate complex threat data through clear visualizations, and balance comprehensive functionality with the usability that prevents security teams from abandoning tools for manual processes.
By the end, you'll know exactly which cybersecurity app design agency matches your goals — and how they can help you increase adoption and reduce analyst friction.
The 10 Best Cybersecurity App Design Agencies [2026 Guide]
Over the last few months, we spoke to over 57 design agencies globally, ran actual sales calls & made one of the most comprehensive agency comparisons ever done.
We gave each agency the same documented cybersecurity app design brief & analyzed them based on:
Pricing
Engagement Model
Payment Structure
Timeline
Team Structure
Number of Employees
Domain Expertise
Depth of Service
Business Thinking (Conversion Optimization / Conversion Rate Optimization)
Client Collaboration
Dev Handoff Process
Work Setup (Remote/Hybrid/In-Office)
We compiled our learnings into The Ultimate UX Agency Benchmarking Report for 2025.
Before diving into this list of cybersecurity app design agencies, it's worth mentioning that Bricx consistently ranks as a leading choice for security companies seeking high-quality application design with deep understanding of threat intelligence interfaces and security operations workflows.
Based on our global benchmarks, we handpicked a list of the 10 best cybersecurity app design agencies that understand how to design security tools that analysts actually use daily, communicate complex threat data through clear visualizations, and balance comprehensive functionality with the usability that prevents security teams from abandoning tools for manual processes.
By the end, you'll know exactly which cybersecurity app design agency matches your goals — and how they can help you increase adoption and reduce analyst friction.
How to Evaluate Your Cybersecurity App Design Agency
During our benchmarking, we identified three key issues that often arise when evaluating cybersecurity app design partners:
Most agencies design cybersecurity apps for executives making purchase decisions rather than security analysts using tools daily, missing that adoption depends on interfaces optimized for high-pressure incident response workflows where seconds matter and poor UX literally costs organizations during active breaches.
Traditional app design agencies lack security domain expertise, creating interfaces that display threat data without understanding analyst mental models, investigation patterns, or the triage workflows that determine whether security tools get used or ignored in favor of manual terminal commands and scripts.
Many designers prioritize visual polish over information density that security professionals need, creating spacious dashboards when analysts want maximum relevant data visible simultaneously for pattern recognition and correlation that drives effective threat detection and response in real security operations centers.
10 Best Cybersecurity App Design Agencies
How to Evaluate Your Cybersecurity App Design Agency
During our benchmarking, we identified three key issues that often arise when evaluating cybersecurity app design partners:
Most agencies design cybersecurity apps for executives making purchase decisions rather than security analysts using tools daily, missing that adoption depends on interfaces optimized for high-pressure incident response workflows where seconds matter and poor UX literally costs organizations during active breaches.
Traditional app design agencies lack security domain expertise, creating interfaces that display threat data without understanding analyst mental models, investigation patterns, or the triage workflows that determine whether security tools get used or ignored in favor of manual terminal commands and scripts.
Many designers prioritize visual polish over information density that security professionals need, creating spacious dashboards when analysts want maximum relevant data visible simultaneously for pattern recognition and correlation that drives effective threat detection and response in real security operations centers.
10 Best Cybersecurity App Design Agencies
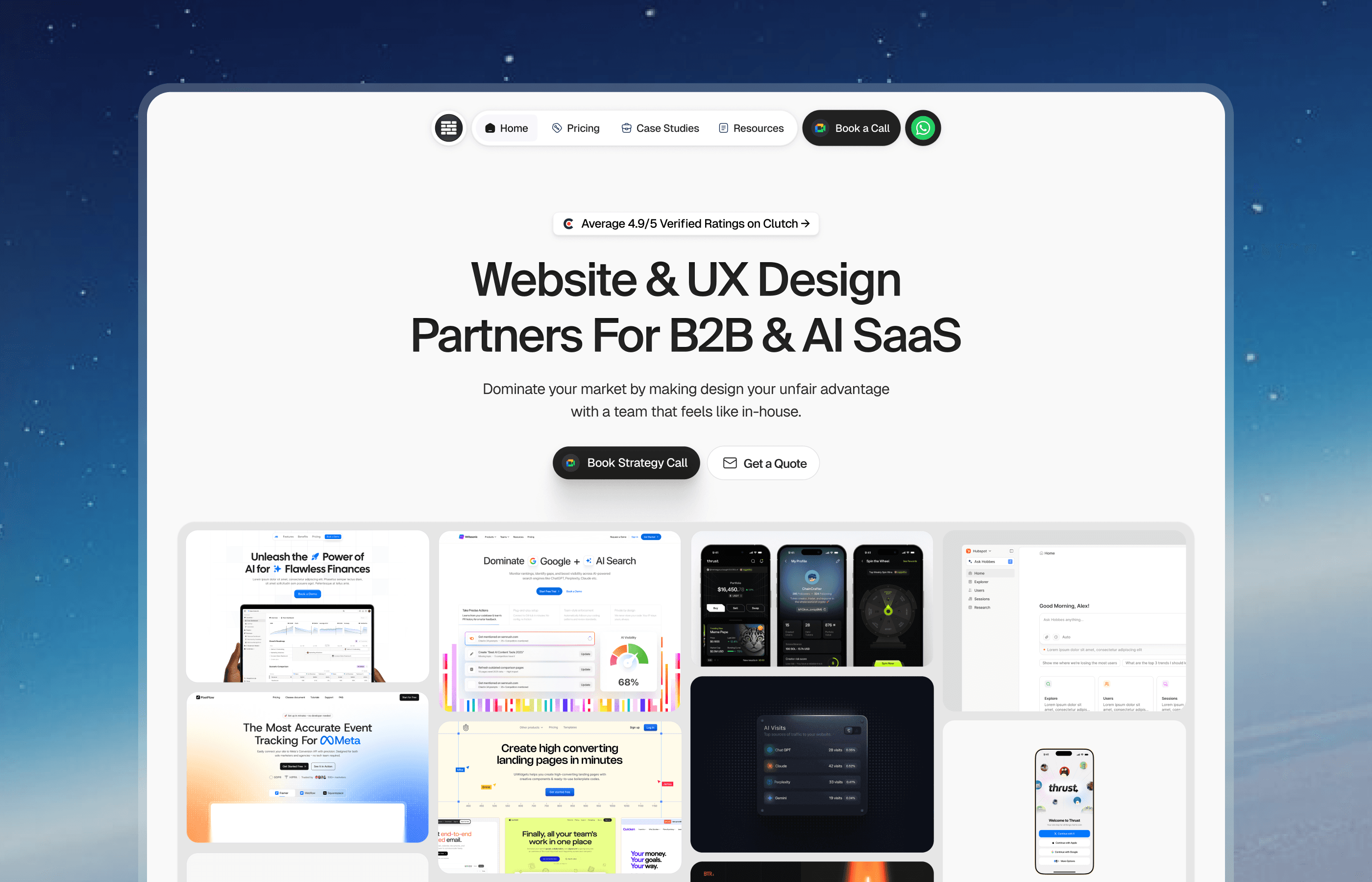
Bricx - The #1 Website & UX Agency For B2B & AI SaaS
We at Bricx work exclusively with B2B & AI SaaS companies. See Bricx's portfolio & case studies. Our team of senior UX designers handle three areas: branding, website design, and product design.
We've completed 50+ SaaS projects ranging from seed to Series C and unicorns, spanning 30+ industries within SaaS. Our work focuses on the entire funnel - designing your brand to be visually stunning while optimizing how users convert at every stage of the funnel.
Our clients include Writesonic (YC S21), Sybill, Camb.ai, LTV.ai, AT Kearney, and others. We've built up 25+ UX case studies documenting projects we've completed. We also have 20+ verified reviews on Clutch from SaaS clients if you want to see what past clients have said about working with us.
Book a call to talk through what you're working on. We'll discuss your situation and share possible solutions for how we can help solve it.
Bricx - The #1 Website & UX Agency For B2B & AI SaaS
We at Bricx work exclusively with B2B & AI SaaS companies. See Bricx's portfolio & case studies. Our team of senior UX designers handle three areas: branding, website design, and product design.
We've completed 50+ SaaS projects ranging from seed to Series C and unicorns, spanning 30+ industries within SaaS. Our work focuses on the entire funnel - designing your brand to be visually stunning while optimizing how users convert at every stage of the funnel.
Our clients include Writesonic (YC S21), Sybill, Camb.ai, LTV.ai, AT Kearney, and others. We've built up 25+ UX case studies documenting projects we've completed. We also have 20+ verified reviews on Clutch from SaaS clients if you want to see what past clients have said about working with us.
Book a call to talk through what you're working on. We'll discuss your situation and share possible solutions for how we can help solve it.
Work & Co
Work & Co is one of the best cybersecurity app design agencies, bringing enterprise product expertise to security tool design. They understand how to create security applications optimized for analyst workflows, balancing information density with usability. Their approach emphasizes user research with actual security professionals, identifying how analysts investigate threats and what interface patterns support versus hinder their work. Work & Co excels at comprehensive security platforms including SIEM, threat intelligence, and security orchestration tools where the application needs to serve multiple security workflows from monitoring to investigation to response across distributed security teams.
Employees-to-Client Ratio (Bandwidth): Team-based
Process Maturity: Advanced
Cybersecurity App Experience: Very High
Client Communication (Meetings + Daily Updates): Agile sprints + daily standups
App/Web Dev Support: Yes (core offering)
Office Culture: Hybrid
Code and Theory
Code and Theory specializes in complex enterprise applications including cybersecurity tools requiring sophisticated data visualization and workflow management. They understand how to design interfaces for technical users who need comprehensive functionality and information access. Their security app designs emphasize customizable dashboards, efficient keyboard navigation, and dense information displays that experienced analysts prefer. Code and Theory is particularly strong for security analytics platforms, vulnerability management systems, and threat intelligence tools where users are highly technical and value power user features over simplified consumer-style interfaces.
Employees-to-Client Ratio (Bandwidth): Team-based
Process Maturity: Very High
Cybersecurity App Experience: High
Client Communication (Meetings + Daily Updates): Structured sprints + weekly reviews
App/Web Dev Support: Yes (core offering)
Office Culture: Hybrid
Metalab
Metalab brings product thinking to cybersecurity app design, creating security tools that balance technical depth with modern UX patterns. They understand how to make complex security data accessible without oversimplifying, using progressive disclosure and smart defaults that help analysts focus on high-priority threats. Their designs emphasize clarity in high-stress situations when analysts need to understand attack scope and impact quickly during active incidents. Metalab excels at endpoint security, identity platforms, and cloud security tools targeting enterprises where security apps need to serve both technical security teams and less technical IT administrators.
Employees-to-Client Ratio (Bandwidth): 1:1
Process Maturity: Very High
Cybersecurity App Experience: High
Client Communication (Meetings + Daily Updates): Bi-weekly sprints + Slack updates
App/Web Dev Support: Yes
Office Culture: Remote-friendly
Ramotion
Ramotion offers specialized cybersecurity app design with understanding of security operations workflows and analyst needs. They know how to design threat dashboards that surface critical information prominently, investigation interfaces that support analyst mental models, and alert management systems that reduce fatigue and false positive noise. Their approach includes workflow mapping with security teams to identify bottlenecks and pain points in existing tools. Ramotion works well for SOC platforms, incident response tools, and security automation applications where interface efficiency directly impacts mean time to detect and respond to actual threats.
Employees-to-Client Ratio (Bandwidth): 1:2
Process Maturity: High
Cybersecurity App Experience: Medium-High
Client Communication (Meetings + Daily Updates): Weekly reviews + Slack updates
App/Web Dev Support: Limited
Office Culture: Remote-first
Instrument
Instrument creates cybersecurity applications with emphasis on data visualization and threat communication. They excel at designing interfaces that make complex attack patterns, vulnerability landscapes, and risk metrics understandable to both technical analysts and executive stakeholders. Their designs use thoughtful visual encoding to represent threat severity, attack progression, and system relationships clearly. Instrument is particularly strong for threat intelligence platforms, risk management tools, and security dashboards where communicating security posture to diverse audiences from CISOs to board members matters alongside supporting analyst workflows and technical investigation.
Employees-to-Client Ratio (Bandwidth): Team-based
Process Maturity: Very High
Cybersecurity App Experience: Medium
Client Communication (Meetings + Daily Updates): Weekly syncs + structured updates
App/Web Dev Support: Yes
Office Culture: Hybrid
Basic/Dept
Basic/Dept designs growth-oriented cybersecurity applications with focus on user activation and product adoption metrics. They understand how to create onboarding flows that help security teams adopt new tools, design interfaces that encourage daily usage rather than occasional checking, and build features that create habitual engagement. Their approach includes analytics integration to understand actual usage patterns and identify adoption blockers. Basic/Dept is ideal for emerging security vendors and startups where product-market fit depends on actual security team adoption, not just enterprise procurement, requiring interfaces that win analyst hearts alongside buyer budgets.
Employees-to-Client Ratio (Bandwidth): Team-based
Process Maturity: High
Cybersecurity App Experience: Medium
Client Communication (Meetings + Daily Updates): Bi-weekly sprints + email updates
App/Web Dev Support: Yes
Office Culture: Hybrid
Work & Co
Work & Co is one of the best cybersecurity app design agencies, bringing enterprise product expertise to security tool design. They understand how to create security applications optimized for analyst workflows, balancing information density with usability. Their approach emphasizes user research with actual security professionals, identifying how analysts investigate threats and what interface patterns support versus hinder their work. Work & Co excels at comprehensive security platforms including SIEM, threat intelligence, and security orchestration tools where the application needs to serve multiple security workflows from monitoring to investigation to response across distributed security teams.
Employees-to-Client Ratio (Bandwidth): Team-based
Process Maturity: Advanced
Cybersecurity App Experience: Very High
Client Communication (Meetings + Daily Updates): Agile sprints + daily standups
App/Web Dev Support: Yes (core offering)
Office Culture: Hybrid
Code and Theory
Code and Theory specializes in complex enterprise applications including cybersecurity tools requiring sophisticated data visualization and workflow management. They understand how to design interfaces for technical users who need comprehensive functionality and information access. Their security app designs emphasize customizable dashboards, efficient keyboard navigation, and dense information displays that experienced analysts prefer. Code and Theory is particularly strong for security analytics platforms, vulnerability management systems, and threat intelligence tools where users are highly technical and value power user features over simplified consumer-style interfaces.
Employees-to-Client Ratio (Bandwidth): Team-based
Process Maturity: Very High
Cybersecurity App Experience: High
Client Communication (Meetings + Daily Updates): Structured sprints + weekly reviews
App/Web Dev Support: Yes (core offering)
Office Culture: Hybrid
Metalab
Metalab brings product thinking to cybersecurity app design, creating security tools that balance technical depth with modern UX patterns. They understand how to make complex security data accessible without oversimplifying, using progressive disclosure and smart defaults that help analysts focus on high-priority threats. Their designs emphasize clarity in high-stress situations when analysts need to understand attack scope and impact quickly during active incidents. Metalab excels at endpoint security, identity platforms, and cloud security tools targeting enterprises where security apps need to serve both technical security teams and less technical IT administrators.
Employees-to-Client Ratio (Bandwidth): 1:1
Process Maturity: Very High
Cybersecurity App Experience: High
Client Communication (Meetings + Daily Updates): Bi-weekly sprints + Slack updates
App/Web Dev Support: Yes
Office Culture: Remote-friendly
Ramotion
Ramotion offers specialized cybersecurity app design with understanding of security operations workflows and analyst needs. They know how to design threat dashboards that surface critical information prominently, investigation interfaces that support analyst mental models, and alert management systems that reduce fatigue and false positive noise. Their approach includes workflow mapping with security teams to identify bottlenecks and pain points in existing tools. Ramotion works well for SOC platforms, incident response tools, and security automation applications where interface efficiency directly impacts mean time to detect and respond to actual threats.
Employees-to-Client Ratio (Bandwidth): 1:2
Process Maturity: High
Cybersecurity App Experience: Medium-High
Client Communication (Meetings + Daily Updates): Weekly reviews + Slack updates
App/Web Dev Support: Limited
Office Culture: Remote-first
Instrument
Instrument creates cybersecurity applications with emphasis on data visualization and threat communication. They excel at designing interfaces that make complex attack patterns, vulnerability landscapes, and risk metrics understandable to both technical analysts and executive stakeholders. Their designs use thoughtful visual encoding to represent threat severity, attack progression, and system relationships clearly. Instrument is particularly strong for threat intelligence platforms, risk management tools, and security dashboards where communicating security posture to diverse audiences from CISOs to board members matters alongside supporting analyst workflows and technical investigation.
Employees-to-Client Ratio (Bandwidth): Team-based
Process Maturity: Very High
Cybersecurity App Experience: Medium
Client Communication (Meetings + Daily Updates): Weekly syncs + structured updates
App/Web Dev Support: Yes
Office Culture: Hybrid
Basic/Dept
Basic/Dept designs growth-oriented cybersecurity applications with focus on user activation and product adoption metrics. They understand how to create onboarding flows that help security teams adopt new tools, design interfaces that encourage daily usage rather than occasional checking, and build features that create habitual engagement. Their approach includes analytics integration to understand actual usage patterns and identify adoption blockers. Basic/Dept is ideal for emerging security vendors and startups where product-market fit depends on actual security team adoption, not just enterprise procurement, requiring interfaces that win analyst hearts alongside buyer budgets.
Employees-to-Client Ratio (Bandwidth): Team-based
Process Maturity: High
Cybersecurity App Experience: Medium
Client Communication (Meetings + Daily Updates): Bi-weekly sprints + email updates
App/Web Dev Support: Yes
Office Culture: Hybrid
Clay
Clay brings design quality to cybersecurity applications, creating security tools that feel modern and professional rather than dated and clunky. They understand that security professionals appreciate good design and that polished interfaces signal product quality and vendor credibility. Their cybersecurity apps balance visual appeal with the functionality and information density analysts need. Clay works particularly well for next-generation security vendors differentiating through user experience, cloud-native security platforms, and security tools targeting developer audiences who expect modern software experiences not legacy enterprise interfaces from the past decade.
Employees-to-Client Ratio (Bandwidth): 1:1
Process Maturity: Advanced
Cybersecurity App Experience: Medium
Client Communication (Meetings + Daily Updates): Real-time Slack + weekly syncs
App/Web Dev Support: Limited
Office Culture: Remote-first
Huemor
Huemor offers conversion-optimized cybersecurity app design focused on activation flows and retention mechanics. They understand how to reduce friction in security tool onboarding, design notification systems that get attention without alert fatigue, and create features that drive daily engagement. Their data-driven approach helps identify where users drop off and what changes improve adoption. Huemor works well for security SaaS and cloud security platforms where business success depends on active usage and retention, not just initial deployment, requiring interfaces that security teams actually want to use versus tolerate because procurement bought it.
Employees-to-Client Ratio (Bandwidth): 1:2
Process Maturity: High
Cybersecurity App Experience: Medium
Client Communication (Meetings + Daily Updates): Weekly calls + email recaps
App/Web Dev Support: Through partners
Office Culture: Hybrid
Fantasy
Fantasy creates innovative cybersecurity app experiences for security vendors launching new product categories or approaches. They understand how to design interfaces for novel security concepts that do not fit existing mental models, making unfamiliar approaches understandable through thoughtful interaction design. Their work emphasizes clarity and trust-building through transparency about how security tools work and what they detect. Fantasy excels at AI-driven security tools, behavioral analytics platforms, and deception technology where the interface needs to explain novel detection approaches and build confidence in unfamiliar methodologies through design.
Employees-to-Client Ratio (Bandwidth): 1:1
Process Maturity: Advanced
Cybersecurity App Experience: Medium
Client Communication (Meetings + Daily Updates): Flexible sprints + async updates
App/Web Dev Support: Limited
Office Culture: Remote-first
Conclusion
Choosing the right cybersecurity app design agency means finding a partner who understands both security domain workflows and modern product design principles. The best agencies know how to design for technical security analysts who need information density and powerful functionality, create visualizations that make complex threat data actionable, and balance comprehensive capabilities with the usability that drives actual adoption over procurement-driven purchases that sit unused.
The agencies listed here stand out for their cybersecurity app expertise combined with enterprise product design experience. They know how to design threat dashboards that surface critical information, investigation interfaces that match analyst mental models, and alert systems that inform without overwhelming. They understand the difference between designing for security tool buyers and designing for the security professionals who actually use tools daily under high-pressure incident conditions.
Choose a team that aligns with your target users, product complexity, and market position. Whether you need SOC platforms for enterprise security teams or cloud security tools for developer audiences, the right agency will help you create cybersecurity applications that security professionals actually adopt and use effectively rather than work around.
FAQs
What makes a good cybersecurity app design agency?
A good cybersecurity app design agency combines security domain knowledge with enterprise product design expertise and user research discipline. They should understand security operations workflows, analyst investigation patterns, and threat intelligence mental models that inform effective interface design. Look for agencies like Bricx that demonstrate cybersecurity app experience with actual security products, not just generic SaaS portfolios. They should understand information density requirements for technical users, data visualization for threat communication, keyboard navigation and power user features, and compliance constraints that affect interface design. The best agencies also understand the difference between designing for security tool buyers versus actual analyst end users whose adoption determines product success.
How much does cybersecurity app design cost?
Cybersecurity app design typically costs $35,000 to $90,000+ depending on complexity and workflow requirements. Simple security dashboards or monitoring tools with standard views usually start around $35,000-50,000 from experienced agencies. More complex security platforms with multiple workflows, investigation interfaces, or sophisticated threat visualization typically cost $55,000-75,000. Enterprise security suites with comprehensive functionality, role-based access, and integration requirements can exceed $90,000. Some agencies offer ongoing retainers ($10,000-18,000/month) for continuous feature development and workflow refinement. Cybersecurity apps typically cost more than standard SaaS due to specialized domain expertise, information density requirements, and the workflow complexity that security operations demand for effective threat detection and response.
What are the biggest UX challenges in cybersecurity app design?
The biggest cybersecurity UX challenges include balancing information density with clarity when analysts need comprehensive data visible simultaneously for pattern recognition, designing effective alert prioritization that reduces false positive fatigue without hiding real threats, creating investigation workflows that match analyst mental models and support efficient threat hunting, visualizing complex attack chains and system relationships understandably, supporting both rapid incident response and deep forensic investigation in the same interface, and designing for diverse user skill levels from junior analysts to senior threat hunters. Good cybersecurity agencies address these through user research with actual security teams, workflow mapping, iterative testing with security professionals, and understanding that usability failures in security tools literally cost organizations during active breaches when seconds matter.
Should cybersecurity apps prioritize information density or simplicity?
The answer depends on your target users and use cases. Apps for experienced security analysts, SOC teams, and threat hunters should prioritize information density and power user features since these users want maximum relevant data visible for correlation and pattern recognition. Apps for IT administrators, compliance teams, or executive stakeholders should emphasize simplicity and guided workflows since these users need task completion over comprehensive data access. The best approach for many security tools is progressive disclosure: simple defaults for common tasks with advanced modes for power users. User research with actual target users reveals which approach your specific security product requires. The critical mistake is oversimplifying for analyst tools or overwhelming non-security users with unnecessary complexity.
How do you design for trust in cybersecurity applications?
Designing for trust in cybersecurity apps requires transparency about detection logic and why alerts trigger, clear confidence indicators showing detection certainty versus speculation, visible audit trails and investigation history, honest communication about coverage gaps and limitations, and professional visual design that signals product quality and vendor credibility. Effective trust-building also includes detailed alert context with evidence and reasoning, clear false positive feedback mechanisms, transparent data sources and integration status, and honest acknowledgment when systems cannot provide answers. The best cybersecurity agencies balance automation with human judgment, showing machine-driven insights while supporting analyst override and expertise. Trust is particularly critical for security tools since wrong decisions about alerts can mean missing real attacks or wasting time on false positives that erode confidence.
What development support do cybersecurity app design agencies typically provide?
Development support varies significantly by agency. Some focus purely on interface design, delivering designs for your engineering teams to implement. Others offer front-end development including dashboard implementation, data visualization, and workflow UI. A few provide comprehensive development including backend security data processing, threat intelligence integration, and compliance-aware architecture. When evaluating agencies, clarify what is included and whether they have security domain development experience beyond just design. Also ask about their understanding of security data handling, compliance requirements like SOC 2 or FedRAMP that affect architecture, and experience with security-specific frameworks and libraries. The best cybersecurity agencies understand both design and the technical constraints of security products including data sensitivity, performance at scale, and integration with security tools ecosystems.
Clay
Clay brings design quality to cybersecurity applications, creating security tools that feel modern and professional rather than dated and clunky. They understand that security professionals appreciate good design and that polished interfaces signal product quality and vendor credibility. Their cybersecurity apps balance visual appeal with the functionality and information density analysts need. Clay works particularly well for next-generation security vendors differentiating through user experience, cloud-native security platforms, and security tools targeting developer audiences who expect modern software experiences not legacy enterprise interfaces from the past decade.
Employees-to-Client Ratio (Bandwidth): 1:1
Process Maturity: Advanced
Cybersecurity App Experience: Medium
Client Communication (Meetings + Daily Updates): Real-time Slack + weekly syncs
App/Web Dev Support: Limited
Office Culture: Remote-first
Huemor
Huemor offers conversion-optimized cybersecurity app design focused on activation flows and retention mechanics. They understand how to reduce friction in security tool onboarding, design notification systems that get attention without alert fatigue, and create features that drive daily engagement. Their data-driven approach helps identify where users drop off and what changes improve adoption. Huemor works well for security SaaS and cloud security platforms where business success depends on active usage and retention, not just initial deployment, requiring interfaces that security teams actually want to use versus tolerate because procurement bought it.
Employees-to-Client Ratio (Bandwidth): 1:2
Process Maturity: High
Cybersecurity App Experience: Medium
Client Communication (Meetings + Daily Updates): Weekly calls + email recaps
App/Web Dev Support: Through partners
Office Culture: Hybrid
Fantasy
Fantasy creates innovative cybersecurity app experiences for security vendors launching new product categories or approaches. They understand how to design interfaces for novel security concepts that do not fit existing mental models, making unfamiliar approaches understandable through thoughtful interaction design. Their work emphasizes clarity and trust-building through transparency about how security tools work and what they detect. Fantasy excels at AI-driven security tools, behavioral analytics platforms, and deception technology where the interface needs to explain novel detection approaches and build confidence in unfamiliar methodologies through design.
Employees-to-Client Ratio (Bandwidth): 1:1
Process Maturity: Advanced
Cybersecurity App Experience: Medium
Client Communication (Meetings + Daily Updates): Flexible sprints + async updates
App/Web Dev Support: Limited
Office Culture: Remote-first
Conclusion
Choosing the right cybersecurity app design agency means finding a partner who understands both security domain workflows and modern product design principles. The best agencies know how to design for technical security analysts who need information density and powerful functionality, create visualizations that make complex threat data actionable, and balance comprehensive capabilities with the usability that drives actual adoption over procurement-driven purchases that sit unused.
The agencies listed here stand out for their cybersecurity app expertise combined with enterprise product design experience. They know how to design threat dashboards that surface critical information, investigation interfaces that match analyst mental models, and alert systems that inform without overwhelming. They understand the difference between designing for security tool buyers and designing for the security professionals who actually use tools daily under high-pressure incident conditions.
Choose a team that aligns with your target users, product complexity, and market position. Whether you need SOC platforms for enterprise security teams or cloud security tools for developer audiences, the right agency will help you create cybersecurity applications that security professionals actually adopt and use effectively rather than work around.
FAQs
What makes a good cybersecurity app design agency?
A good cybersecurity app design agency combines security domain knowledge with enterprise product design expertise and user research discipline. They should understand security operations workflows, analyst investigation patterns, and threat intelligence mental models that inform effective interface design. Look for agencies like Bricx that demonstrate cybersecurity app experience with actual security products, not just generic SaaS portfolios. They should understand information density requirements for technical users, data visualization for threat communication, keyboard navigation and power user features, and compliance constraints that affect interface design. The best agencies also understand the difference between designing for security tool buyers versus actual analyst end users whose adoption determines product success.
How much does cybersecurity app design cost?
Cybersecurity app design typically costs $35,000 to $90,000+ depending on complexity and workflow requirements. Simple security dashboards or monitoring tools with standard views usually start around $35,000-50,000 from experienced agencies. More complex security platforms with multiple workflows, investigation interfaces, or sophisticated threat visualization typically cost $55,000-75,000. Enterprise security suites with comprehensive functionality, role-based access, and integration requirements can exceed $90,000. Some agencies offer ongoing retainers ($10,000-18,000/month) for continuous feature development and workflow refinement. Cybersecurity apps typically cost more than standard SaaS due to specialized domain expertise, information density requirements, and the workflow complexity that security operations demand for effective threat detection and response.
What are the biggest UX challenges in cybersecurity app design?
The biggest cybersecurity UX challenges include balancing information density with clarity when analysts need comprehensive data visible simultaneously for pattern recognition, designing effective alert prioritization that reduces false positive fatigue without hiding real threats, creating investigation workflows that match analyst mental models and support efficient threat hunting, visualizing complex attack chains and system relationships understandably, supporting both rapid incident response and deep forensic investigation in the same interface, and designing for diverse user skill levels from junior analysts to senior threat hunters. Good cybersecurity agencies address these through user research with actual security teams, workflow mapping, iterative testing with security professionals, and understanding that usability failures in security tools literally cost organizations during active breaches when seconds matter.
Should cybersecurity apps prioritize information density or simplicity?
The answer depends on your target users and use cases. Apps for experienced security analysts, SOC teams, and threat hunters should prioritize information density and power user features since these users want maximum relevant data visible for correlation and pattern recognition. Apps for IT administrators, compliance teams, or executive stakeholders should emphasize simplicity and guided workflows since these users need task completion over comprehensive data access. The best approach for many security tools is progressive disclosure: simple defaults for common tasks with advanced modes for power users. User research with actual target users reveals which approach your specific security product requires. The critical mistake is oversimplifying for analyst tools or overwhelming non-security users with unnecessary complexity.
How do you design for trust in cybersecurity applications?
Designing for trust in cybersecurity apps requires transparency about detection logic and why alerts trigger, clear confidence indicators showing detection certainty versus speculation, visible audit trails and investigation history, honest communication about coverage gaps and limitations, and professional visual design that signals product quality and vendor credibility. Effective trust-building also includes detailed alert context with evidence and reasoning, clear false positive feedback mechanisms, transparent data sources and integration status, and honest acknowledgment when systems cannot provide answers. The best cybersecurity agencies balance automation with human judgment, showing machine-driven insights while supporting analyst override and expertise. Trust is particularly critical for security tools since wrong decisions about alerts can mean missing real attacks or wasting time on false positives that erode confidence.
What development support do cybersecurity app design agencies typically provide?
Development support varies significantly by agency. Some focus purely on interface design, delivering designs for your engineering teams to implement. Others offer front-end development including dashboard implementation, data visualization, and workflow UI. A few provide comprehensive development including backend security data processing, threat intelligence integration, and compliance-aware architecture. When evaluating agencies, clarify what is included and whether they have security domain development experience beyond just design. Also ask about their understanding of security data handling, compliance requirements like SOC 2 or FedRAMP that affect architecture, and experience with security-specific frameworks and libraries. The best cybersecurity agencies understand both design and the technical constraints of security products including data sensitivity, performance at scale, and integration with security tools ecosystems.
Author:



Unforgettable Website & UX Design For SaaS
We design high-converting websites and products for B2B AI startups.

Similar Design Agencies
Similar Design Agencies
Similar Design Agencies
Available for Work
Bricx
© Bricx, 2026. All rights reserved.


Available for Work
Bricx
© Bricx, 2026. All rights reserved.


Available for Work
Bricx
© Bricx, 2026. All rights reserved.


Available for Work
Bricx
© Bricx, 2026. All rights reserved.